What is VPN
VPN is short for Virtual Private Network. VPN creates a private network over a public network for encrypted communications.
The VPN gateway implements remote access by encrypting the data packet and converting the target address of the data packet.
VPNs are widely used in enterprise networks because they can be installed on servers, hardware, and software.
VPN is a type of remote access technology that uses a public network to build a private network for users. So what is remote access? When you want to work from home, or when someone from another country wants to work on the company Intranet, such access requests are called remote access.

However, some people will question, why not choose the dial-up line to access the enterprise Intranet directly?
Of course, you can, but it can be a security risk for businesses and individuals.
Some traditional enterprises choose to use leased DDN lines (which provide users with dedicated medium and high speed digital data transmission channels, so that users can use it to organize their own computer communication networks) for remote access, but this kind of equipment is relatively old, and enterprises need to pay more expensive communication costs and equipment maintenance costs.
VPN essentially uses a series of encryption technologies to install a data exchange channel on the public network.
After a VPN server is installed on the Intranet, the Internet is connected to the VPN server when remote users want to access Intranet information. Then the VPN accesses the desired website.
The VPN in the middle transmits information to servers and user devices on both sides while encrypting the data. This encryption process makes much of the data “unreadable” to the outside world as if it were a separate channel, but in fact, a VPN still uses a public network.
The working process of the VPN
The workflow of VPN is very similar to the sealing, transportation, and unpacking of express packages. The workflow of VPN is as follows:
- Protect the host from sending information.
- Select the delivery mode: According to the rules set by the network administrator, decide whether to encrypt the data (packaging and sealing) or directly transmit the data.
- Packing: If encryption is required, the VPN device encrypts all the data (including the data to be transmitted, source IP address, and destination lP address), adds a data signature, and re-encapsulates new data headers (including the security information and initialization parameters required by the destination VPN device).
- Transport: The encapsulated packets are transmitted over the public network through the channel.
- Check and unpack: After the data packet arrives at the destination, the data packet is decrypted (unpack) after checking the digital signature.

In the entire flow, the destination address of the original data packet (VPN destination address) and the remote VPN gateway address are very important, which affect the whole VPN communication.
According to the destination address, the VPN gateway can determine which packets need to be processed, and those packets that do not need to be processed can be directly forwarded. The remote VPN gateway address specifies the destination address (the address at the other end of the VPN channel) to which the processed packets are sent.
Because communication is bidirectional, gateways at both ends of the channel must know the destination address of the packet and the remote VPN gateway address to ensure the correctness and stability of information transmission.
The advantages of VPN
- Convenient and Flexible–VPNs make it possible to work flexibly.
Home and business travel are no longer barriers to not being able to work, and business partners and others can take advantage of locally available high-speed broadband connections to connect to corporate networks.
- Easy for use–VPNs give users a whole new experience.
It provides an Internet infrastructure that is easy to set up so that both new and old users can quickly pick up and easily add to the network.
- Full of Security–VPNs have a higher level of security.
It establishes tunnels. Encryption and identity protocols protect data from outside prying eyes, effectively preventing data theft and other unauthorized devices from reading the data.
- Stable and Efficient–VPNs provide quality service.
Wan traffic is unstable and bandwidth utilization is low, the traffic distribution is polarized. During peak traffic periods, network bottlenecks are caused due to congestion, which greatly affects the transmission of real-time data. However, a large amount of bandwidth is idle during low traffic periods. VPNs use traffic control policies to arrange bandwidth based on priorities to prevent congestion.
- Manageable
VPNs are fully managed by the user, making it easier for everyone else to use it.
- Save money
The cost of traditional long-distance dedicated lines is huge. VPNs only need to connect new nodes and provide the communication rules between new points and other points at a relatively low cost.
The disadvantages of VPN
- Relyon suppliers
Users need to sign a contract with a VPN supplier to keep the service running. Individuals can’t directly interfere with VPN performance. Creating a VPN is a complex process, so it’s important to find a good vendor and sign a reasonable contract.
- Maybe the product is not compatible
VPN products and solutions from different suppliers are sometimes incompatible, driving up the cost of using the device.
- Wireless devices may pose security risks
Any advanced encryption can be breached as users roam between access points.
What is IP VPN
We already know what VPN is. We know that it takes a lot of money and energy to buy the equipment, design and build the lines, and carry out daily maintenance. Even training can be costly. In this case, you need to purchase the VPN service provided by the suppliers. IP VPN is also a service they provide.
Based on the Backbone network owned by the supplier and using the advanced multi-protocol label switching (MPLS) technology, the IP VPN service provides end-to-end service quality assurance and security services for enterprise users to build an internal private network.
Generally, IP VPN service suppliers have professional technical teams and a relatively large operation scale to help users to establish a more mature and stable network, which saves a lot of time and unnecessary capital consumption for users, and at the same time enables users to have a better experience.
Common technologies of IP VPN
- L2TP: Widely used for distributed mobile customers.
- IPSec: It can be used alone or in conjunction with tunneling protocols such as L2TP and GRE, giving users greater flexibility and reliability.
- GRE: An early, mature protocol, which is easy to implement.
- MPLS: A new technology that uses tags to guide data along with an open communication network at a fast and efficient rate. It is used to regulate network resources and improve service quality.
The difference between VPN and IP VPN
VPN and IP VPN have different mechanisms
The tunnel can ensure security. Therefore, IP VPN also uses the channel mechanism to make the encapsulation mode and address information of VPN packets irrelevant to that of the bearer network.
However, while IP VPN is very similar to VPN, they are different.
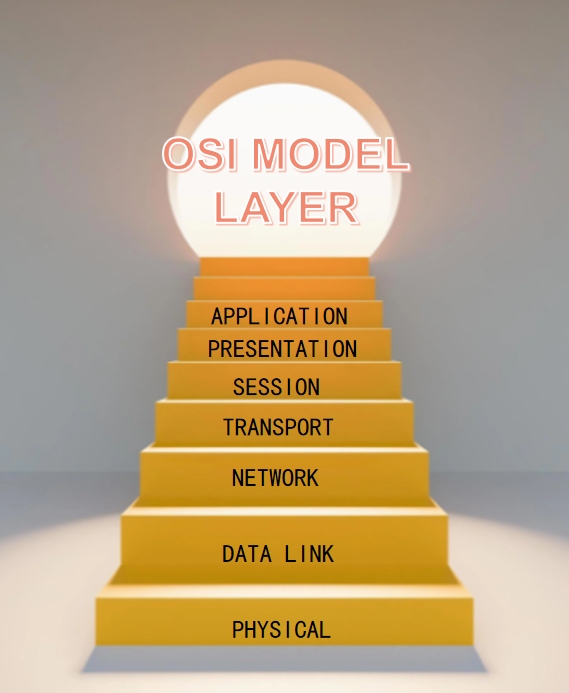
VPNs belong to layer 3 and layer 4 of the OSI model and, as mentioned earlier, build channels over the public network, which means that the VPN still relies on the public network. And no matter how you defend it, using a public network means you may face bandwidth deficits (denial of service) and slow speeds.
However, IP VPN belongs to layer 2, which means that it is off the public network and connects to the site through a private network, which ensures the efficiency and security of data transmission.
VPN and IP VPN apply different circumstances
VPN is recommended if you are working for an individual’s daily life or for a small startup where you don’t need to telecommute. Because A VPN can meet your data transmission and security needs without paying excessive costs for maintenance, resulting in a personal economic burden.
But if it is a large enterprise or a major organization, IPVPN is the best choice. Because IP VPN can meet the demand of access from different places, it is more efficient and more secure. And large enterprises can support the cost of operating an IP VPN.
For suppliers, IP VPN is a business scope with great potential, and improving better IP VPN services is the need of The Times.




 Jolian
Jolian September 8,2021
September 8,2021



