The definition of cookie, what is cookie
Cookie is a plain text file saved in the client, used to record the status of the user’s access to the server. When a user uses a browser on a computer to access a web page, the server will record the user’s current state value, and generate a certificate to the browser, which is recorded in the local computer.
This certificate is a cookie.
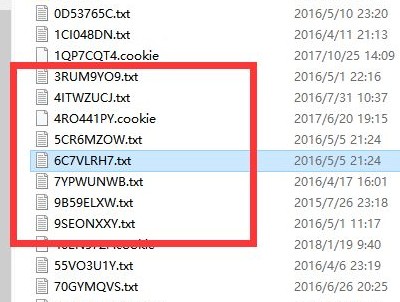
Cookies have a validity period. During the validity period of the cookie, when the user visits the same server again, the browser will send the cookie to the server. The server will identify the cookie to determine the user’s identity, and then provide the user with the corresponding resources and content.
The birth of cookies
With the development of the Internet, people are no longer satisfied with basic web services and have greater demands for the convenience and ease of use of web services. At the same time, it is hoped that the server can record the activity status of different users, even in complex Internet interactions, Can also accurately provide users with resources and content.
As we all know, the transmission of Internet information relies on the HTTP protocol, but the HTTP protocol is stateless. The server cannot determine the user’s identity through the http protocol, nor can it record the user’s status, which causes the user to be unable to obtain the previous information each time they visit. If you want to continue the previous information, you must retransmit it, which is very troublesome and inefficient.
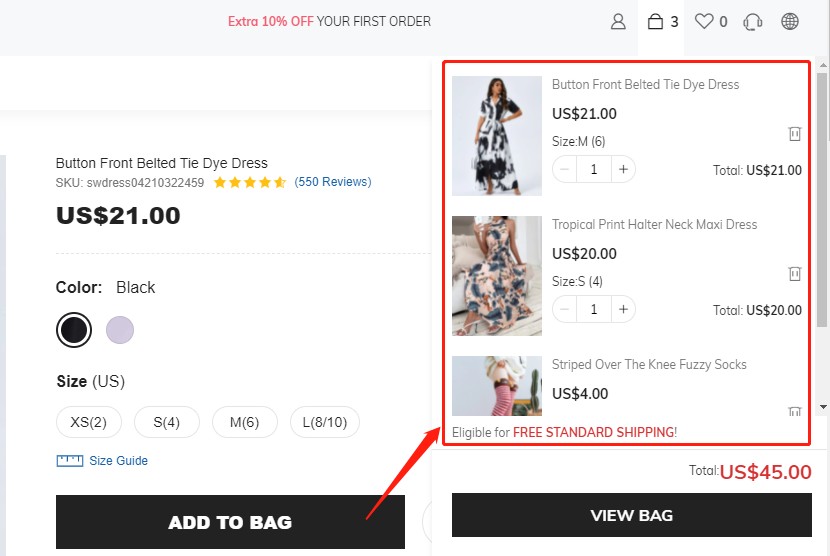
For example, You have carefully selected 10 items on Amazon and put them into the shopping cart. At this time, you accidentally closed Amazon. When you open Amazon again, you definitely hope that the 10 items are still in the shopping cart.
The HTTP protocol cannot help you. But cookies can.
When the demand for dynamic interaction between the client and the server is increasing, technical means to save the state of web services have emerged. The most familiar one is the cookie, and there is another technology called session.
Cookie attributes
A cookie is composed of several attributes, and they respectively record some information, such as the effective time, which domain name is sent to, which path is stored in, and so on. Cookie attributes include Name/Value, Expires, Path, Domain, Secure, Httponly.
The attributes are separated by semicolons and spaces. Each attribute can be set If not set, use the default value.
Detailed introduction of cookie attributes:
Name/Value attribute: Set the name of the cookie and the corresponding value, name it with letters and numbers, and cannot use special characters.
Expires attribute: Set the expiration time of the cookie. During this time, the cookie is valid. The browser will clear the cookie after the time expires. The expires attribute must be a time in GMT format. If the expires attribute is not set, the cookie will be cleared immediately after closing the browser.
Path attribute: Set the path where cookies can be accessed on the website, usually set to “/”, which means that all pages on the site can access cookies.
Domain attribute: Set which websites can access cookies, the domain attribute and path attribute are used together to set which URLs can access cookies.
Secure attribute: The cookie can only be sent under the secure protocol. By default, the cookie does not have the secure attribute. Both the HTTP protocol and the HTTPS protocol can access the cookie. After the secure attribute is set, only the HTTPS protocol can access the cookie.
Httponly attribute: Setting cookies cannot be accessed through forms other than the HTTP protocol. Under normal circumstances, the client can read, modify, and delete cookie information through JavaScript code. After setting the Httponly attribute, JavaScript can no longer access the cookie, which helps to protect the cookie. Will not be maliciously stolen and tampered with.
How cookies work
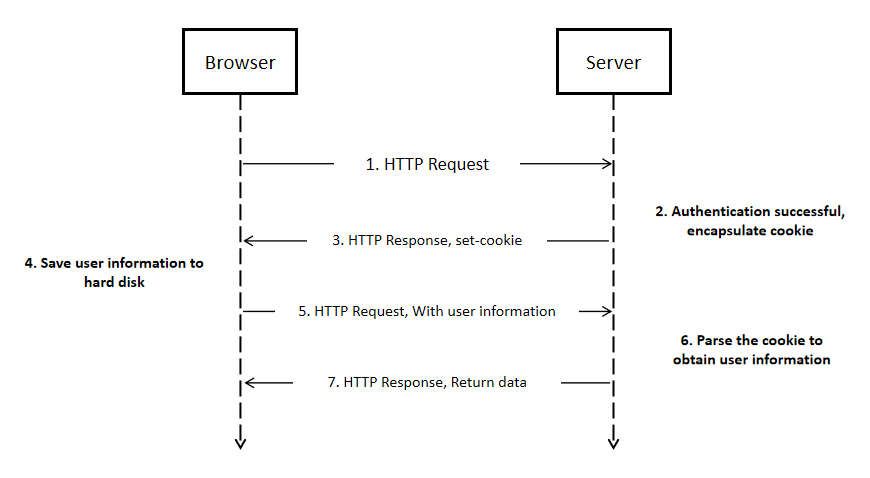
When a user visits a website, the cookie generation will go through the following steps:
Step 1: The client sends a request to the server.
Step 2: After the server receives the client’s request, it will generate a set-cookie head based on the client’s information, and send it back to the client to establish a session.
Step 3: The client receives the information and if it is determined to establish a session, it will store the cookie file on the local hard disk.
Step 4: When the client sends a request to the server again, the browser will look for the corresponding cookie file according to the website domain name, and if found, it will send the cookie content to the server.
Step 5: After the server receives the request containing the cookie, it will generate a page that meets the needs of the client and send it to the client based on the relevant user information stored in the cookie.
The basic operation of cookies
- Set cookies on the client
On the client-side, the cookie can be set through JavaScript, and the value of the cookie can be set by executing the code.
E.g: document.cookie=”expires=Thu, 26 Feb 2116 11:50:25 GMT; domain=www.clonbrowser.com; path=/”;
When we check the cookie panel of the browser, we can see that the expires, domain, path, and other attributes have been set successfully.
Note: The client can set attributes including expires, domain, path, secure, but cannot set Httponly attributes.
- Set cookies on the server
Through the above, we have learned that when the client sends a request to the server, the server will send a set-cookie, which is used by the server to set the cookie.
Note: The server can set all cookie attributes
- Set multiple cookies at the same time
If you want to set the attributes of multiple cookies, you can implement it by repeatedly executing JavaScript code in multiple lines.
- Modify cookie
If you want to modify an attribute of the cookie, you only need to modify the attribute value of the cookie, and the new attribute value will overwrite the old attribute value.
Note: When modifying the cookie, the domain and path attributes must be consistent, otherwise a new cookie will be generated.
- Delete cookie
If you want to delete the cookie, you need to reset the expires attribute of the cookie and set a time in the past, so that the cookie will naturally become invalid.
Security issues with cookies
Why cookies are not secure
Cookies are stored in the user’s local computer. Personal computers are often less secure and can easily be intercepted and stolen by other hackers.
What are the security risks of cookies
- Cookie spoofing
Cookie spoofing is caused by cookie leakage. Cookies are easily discovered and intercepted during network transmission, especially the transmission of HTTP protocol. When hackers get the cookie, they can log in to the corresponding website as a fake user and obtain the user’s privacy information.

- cookie injection
Cookie injection is the opposite of cookie spoofing. Cookie injection allows users to log in to cookies that have been tampered with without their knowledge. Cookie injection requires high technical means. Experts can often achieve precise attacks, which are extremely concealed and difficult to be discovered.
- Malicious cookie code
The cookie itself is an ordinary text file. If you use a special markup language to embed executable code in the cookie, you may further steal user identity information.
How to protect cookie security
Cookies are stored as plain text files on the computer. In theory, attacking cookies will not cause great harm to the user’s computer. However, there are still many hidden dangers in the leakage of cookies. If it is leaked, the user’s web access information will no longer be safe, private Data can be easily stolen.

It is also essential to protect the safety of cookies. Introduce some methods to make your cookies more secure.
- Cookie expiration period becomes shorter
Setting the validity period of the cookie shorter is a simple and effective method, which makes the security of the cookie controllable.
- Set Httponly attribute
The Httponly attribute can prevent the cookie from being accessed by JavaScript, which can improve the security of the cookie.
- Set the secure attribute
The Secure attribute allows cookies to be accessed only by the HTTPS transmission protocol, which is more secure than the HTTP protocol.
- Set complex cookie
- Randomly generate the key value of the cookie
- Use complex cookie naming
- Increase the difficulty of cookie decryption as much as possible, and protect cookie information
- Strengthen the security protection of the database
If the database is sufficiently secure, even if a cookie is leaked, the loss caused will be greatly reduced
- Use session and cookie at the same time
Session and cookie are both methods used to store user web information. The difference is that the cookie is stored on the client-side and the session is stored on the server. While using the cookie to record the information, it can be verified on the server-side through the session, which can be extra insurance.




 Jolian
Jolian July 19,2021
July 19,2021



